The build environment must be based on bullseye. This is achieved by using a docker container to build the .deb packages |
||
|---|---|---|
| group_vars | ||
| innernet-src@9a59ac3094 | ||
| inventory@873e2fd4cf | ||
| roles | ||
| .gitignore | ||
| .gitmodules | ||
| ansible.cfg | ||
| build-debs.sh | ||
| Dockerfile | ||
| fsfe-innernet.png | ||
| open_the_vault.sh | ||
| playbook.yml | ||
| README.md | ||
| vault_passphrase.gpg | ||
| vault_passphrase.gpg.license | ||
Table of Contents
Motivation
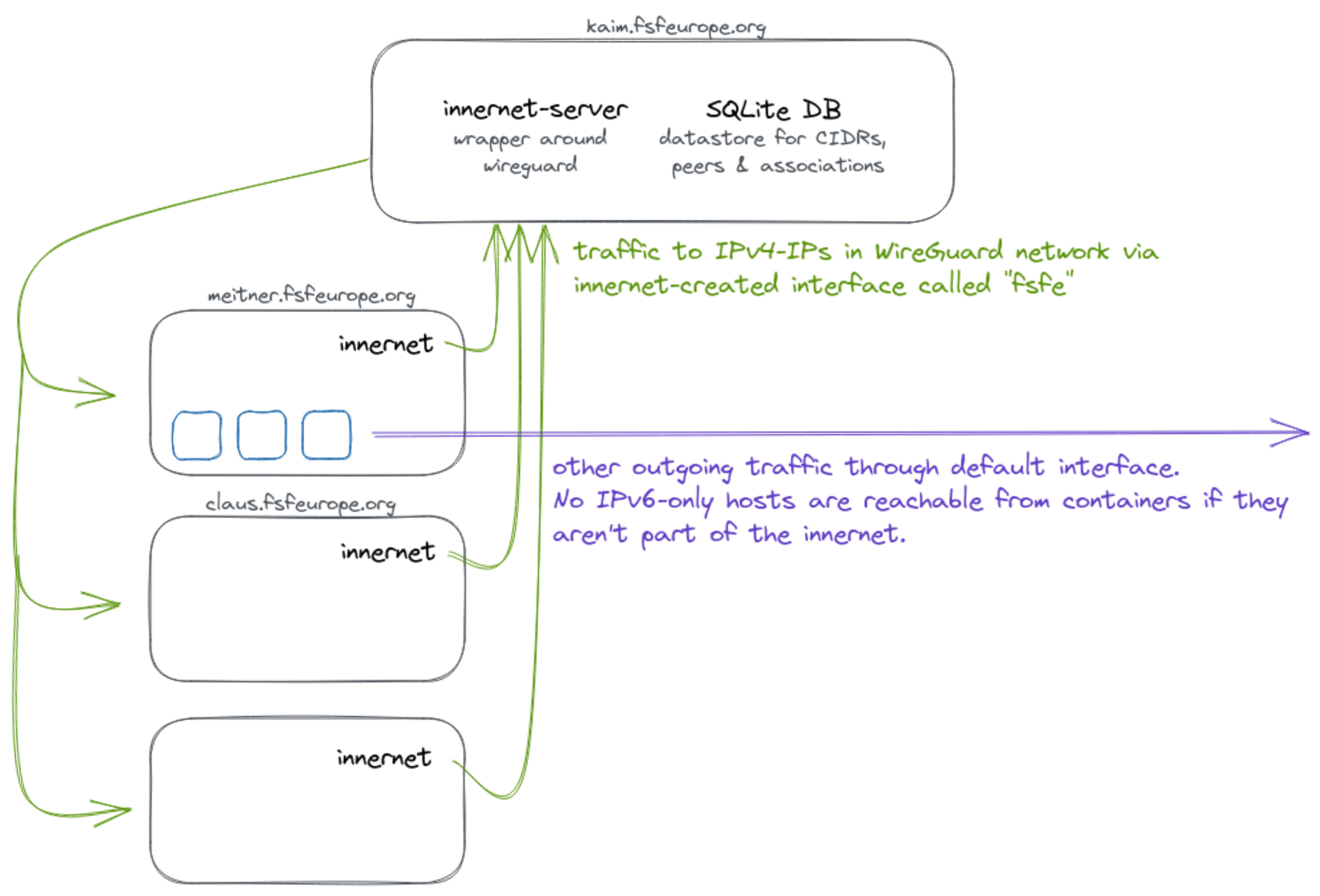
There is a need for some of our servers to connect to other IPv6-only hosts. Since this is not always possible without introducing major painpoints elsewhere, we simply create an internal WireGuard network so that the machines in question can communicate securely using IPv4.
Preparation
Clone the repo
git clone --recurse-submodules git@git.fsfe.org:fsfe-system-hackers/innernet-playbook.git
cd innernet-playbook
Build binaries from submodule at ./innernet-src
Since innernet is new software, it is not yet included in the Debian repositories. Thus, before running the playbook we need to build the innernet and innernet-server binaries. At the moment, we are using 1.5.1, but you can choose any other available version by setting the environment variable accordingly. Please also note that you need cargo-deb installed to successfully compile the Debian packages.
./build-debs.sh
You can learn more about innernet by looking at its source code or reading this informative blog post of its creator.
Preparing ansible
To ensure this playbook works on different machines, pipenv is used to pin the version of ansible. So, to use the same version of Ansible that this playbook was tested with, simply run:
pipenv install --dev # for developing or
pipenv install # for simply running this playbook
pipenv shell
Now, you should be in a shell that is running the correct version of the ansible and ansible-playbook executable.
Execution
Run the playbook
ansible-playbook deploy.yml
Distribute the invitation files
Some invitation files are for humans, so you need to send these files to them securely. I suggest using someting like wormohle.
sudo apt install magic-wormhole
cd roles/client/files
wormhole send <name_of_peer>.toml